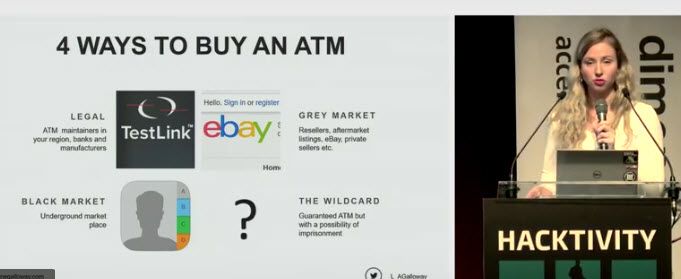
Video - How to buy an ATM - Hacktivity 2017
A video of my talk about the process of buying and hacking an ATM
A video of my talk about the process of buying and hacking an ATM
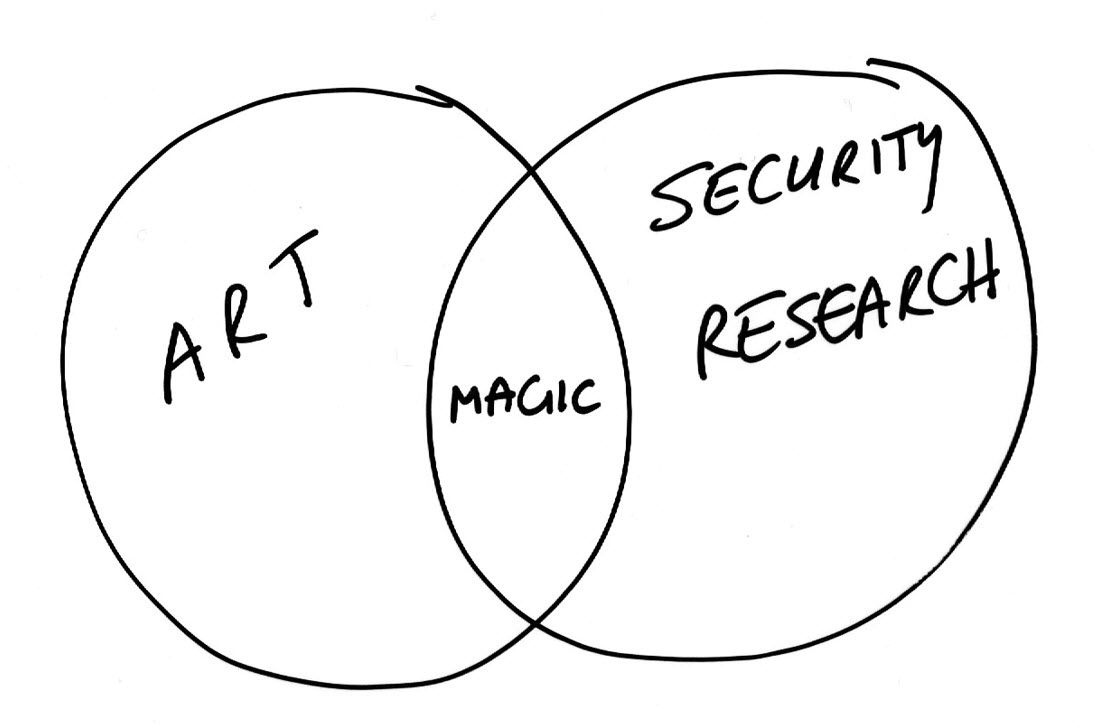
Video of my keynote at Bsides Lisbon 2019, where I discuss my approach to security research.
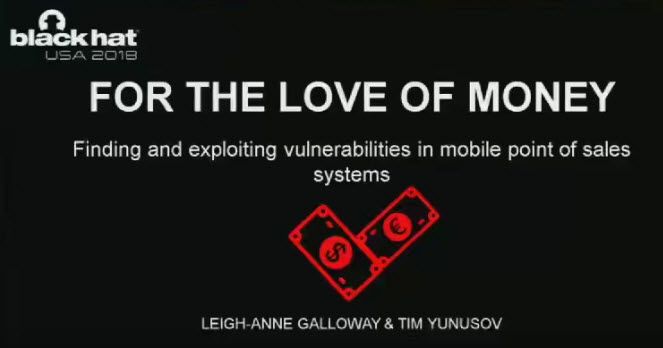
Video of our talk on the vulnerabilities in mobile point of sales terminals.

Video of our Talk "For the Love of Money"

My thoughts on the security conference 8dot8 in Chile, 2017
My thoughts on the security conference Bsides Lisbon, 2017